Ubuntu搭建Ocserv配置路由分流(转)
一、项目准备
1.1、VMware ESXi
1.2、Ubuntu镜像
1.3、OpenConnect客户端
1.4、AnyConnect客户端
1.5、SSH工具
1.5.1、MobaXterm激活
二、部署Ubuntu
Ubuntu系统在VMware ESXi中安装设置请参考 Ubuntu搭建OpenVPN配置分流规则指南!第二步)
Ubuntu系统在VMware ESXi中安装设置请参考 Ubuntu搭建OpenVPN配置分流规则指南!第二步)
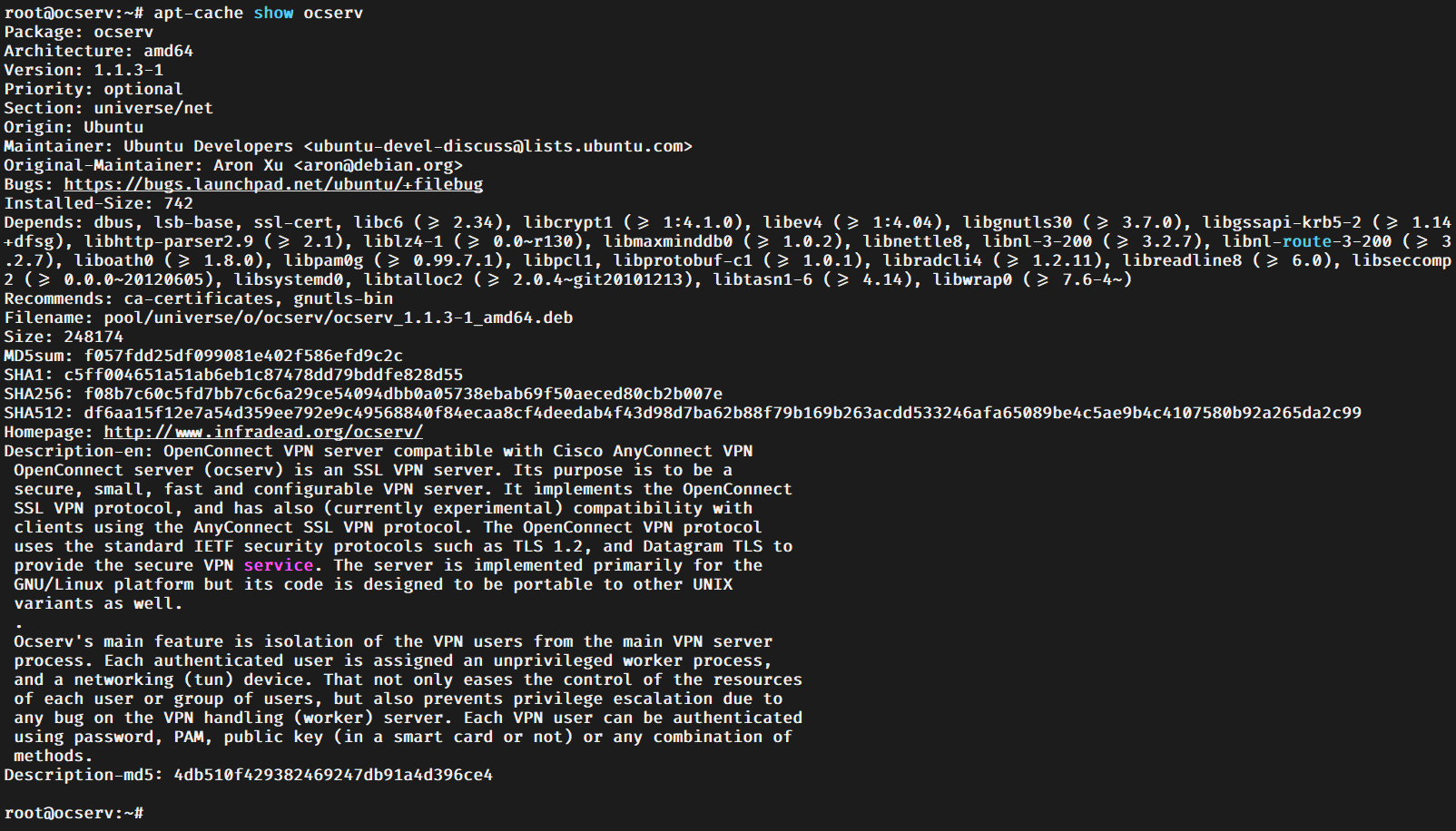
apt-cache show ocserv
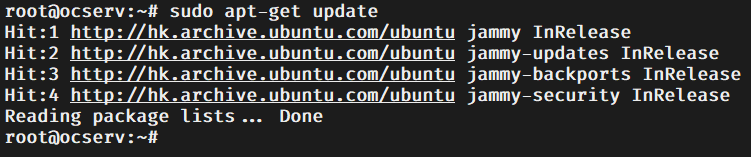
sudo apt-get update
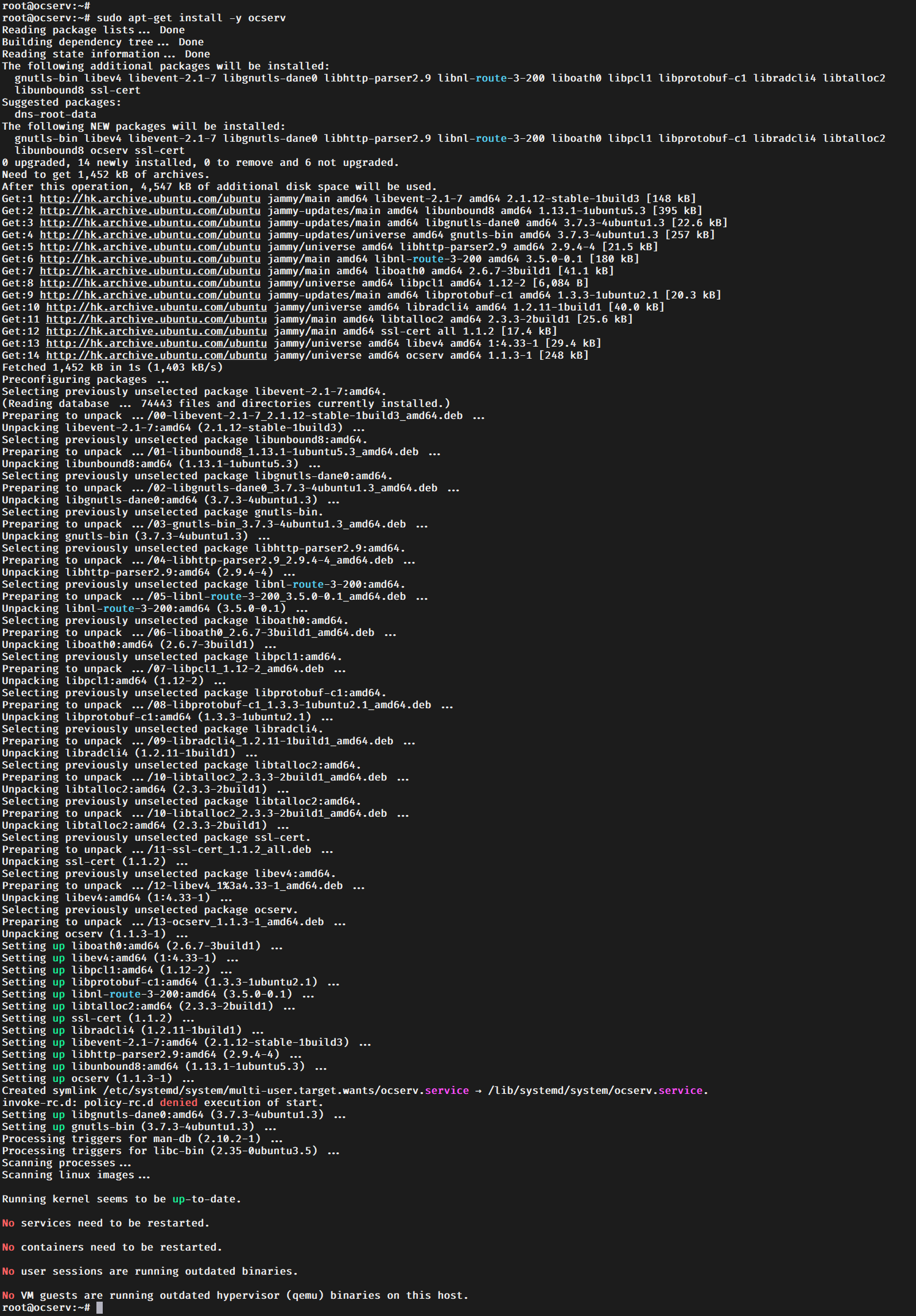
sudo apt-get install -y ocserv
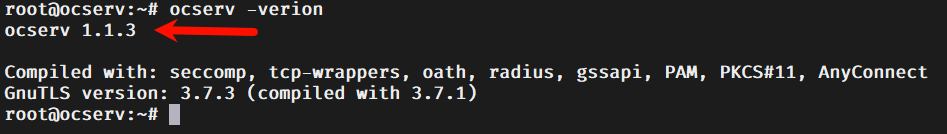
ocserv -version
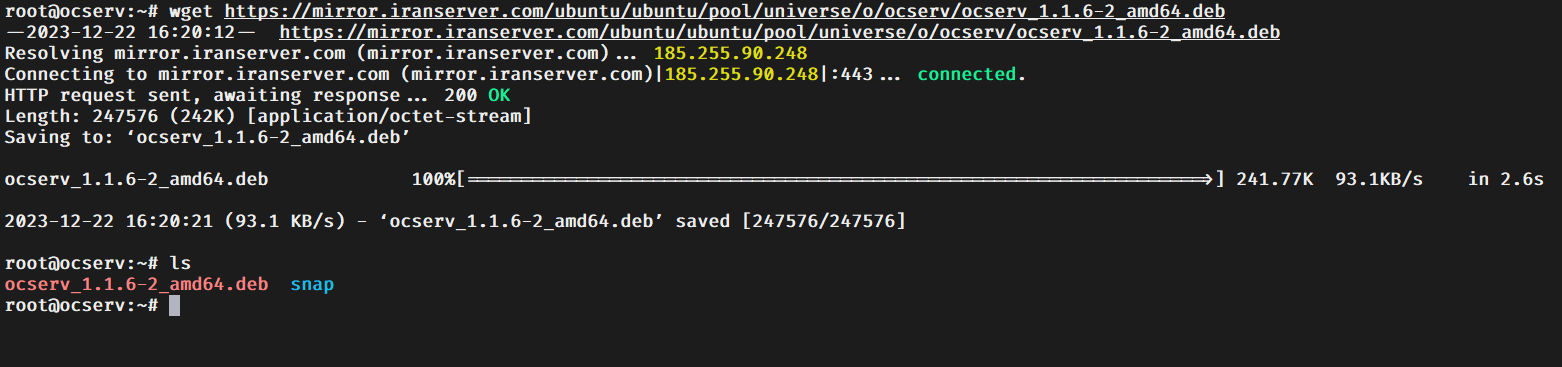
sudo apt-get install -y wget && wget https://mirror.iranserver.com/ubuntu/ubuntu/pool/universe/o/ocserv/ocserv_1.1.6-2_amd64.deb
sudo apt-get install ssl-cert libev4 libhttp-parser2.9 libnl-route-3-200 liboath0 libprotobuf-c1 libradcli4 libtalloc2
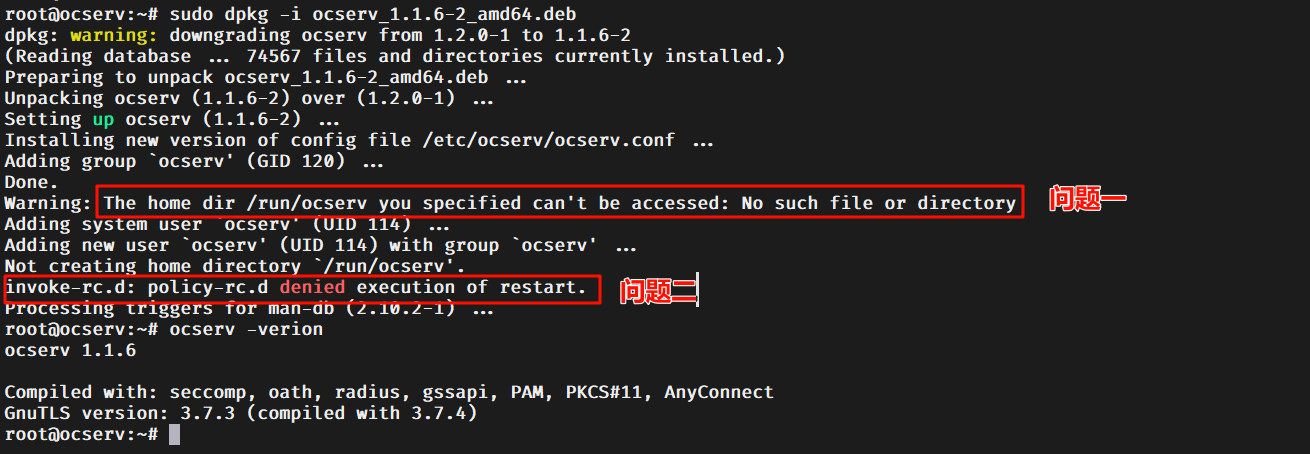
sudo dpkg -i ocserv_1.1.6-2_amd64.deb
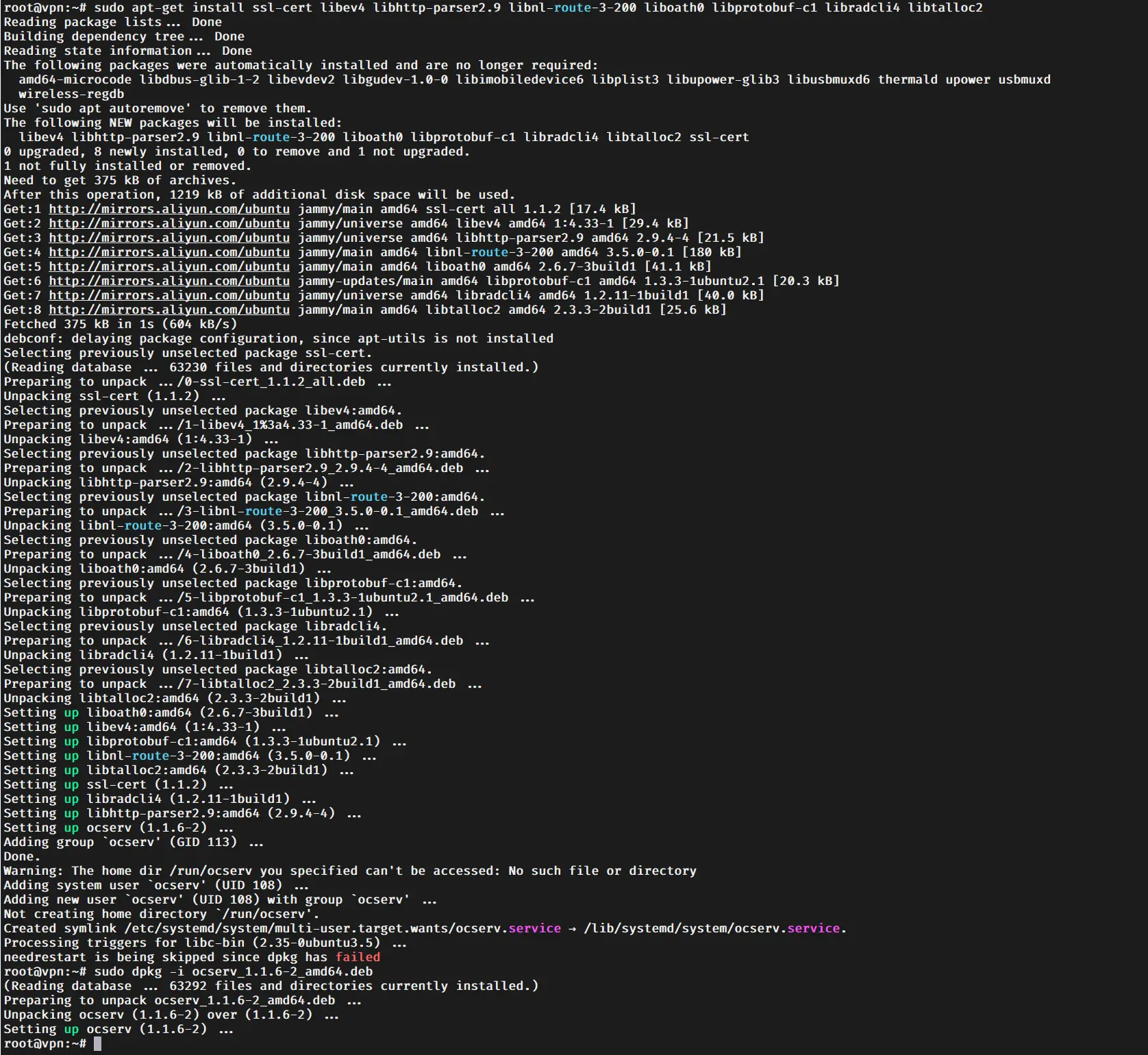
ocserv -version
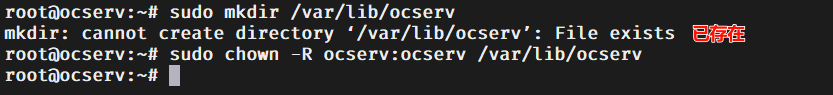
sudo mkdir /var/lib/ocserv
sudo chown -R ocserv:ocserv /var/lib/ocserv
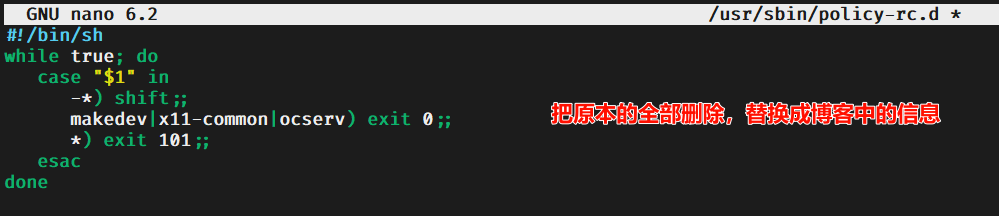
sudo nano /usr/sbin/policy-rc.d
#!/bin/sh
while true; do
case "$1" in
-*) shift;;
makedev|x11-common|ocserv) exit 0;;
*) exit 101;;
esac
done
sudo systemctl restart ocserv
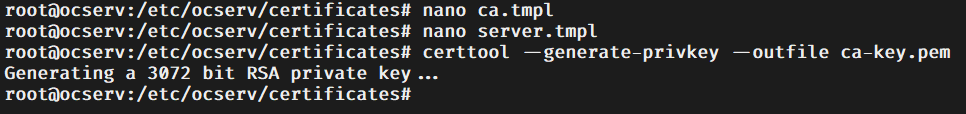
mkdir /etc/ocserv/certificates && cd /etc/ocserv/certificates
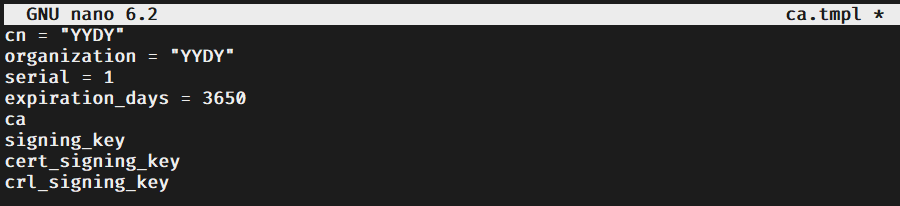
nano ca.tmpl
cn = "Your CA name"
organization = "Your organization name"
serial = 1
expiration_days = 3650
ca
signing_key
cert_signing_key
crl_signing_key
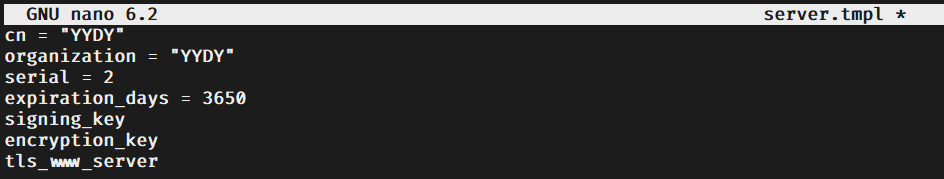
nano server.tmpl
cn = "Your hostname or IP"
organization = "Your organization name"
serial = 2
expiration_days = 3650
signing_key
encryption_key
tls_www_server
sudo apt-get install -y gnutls-bin
certtool --generate-privkey --outfile ca-key.pem
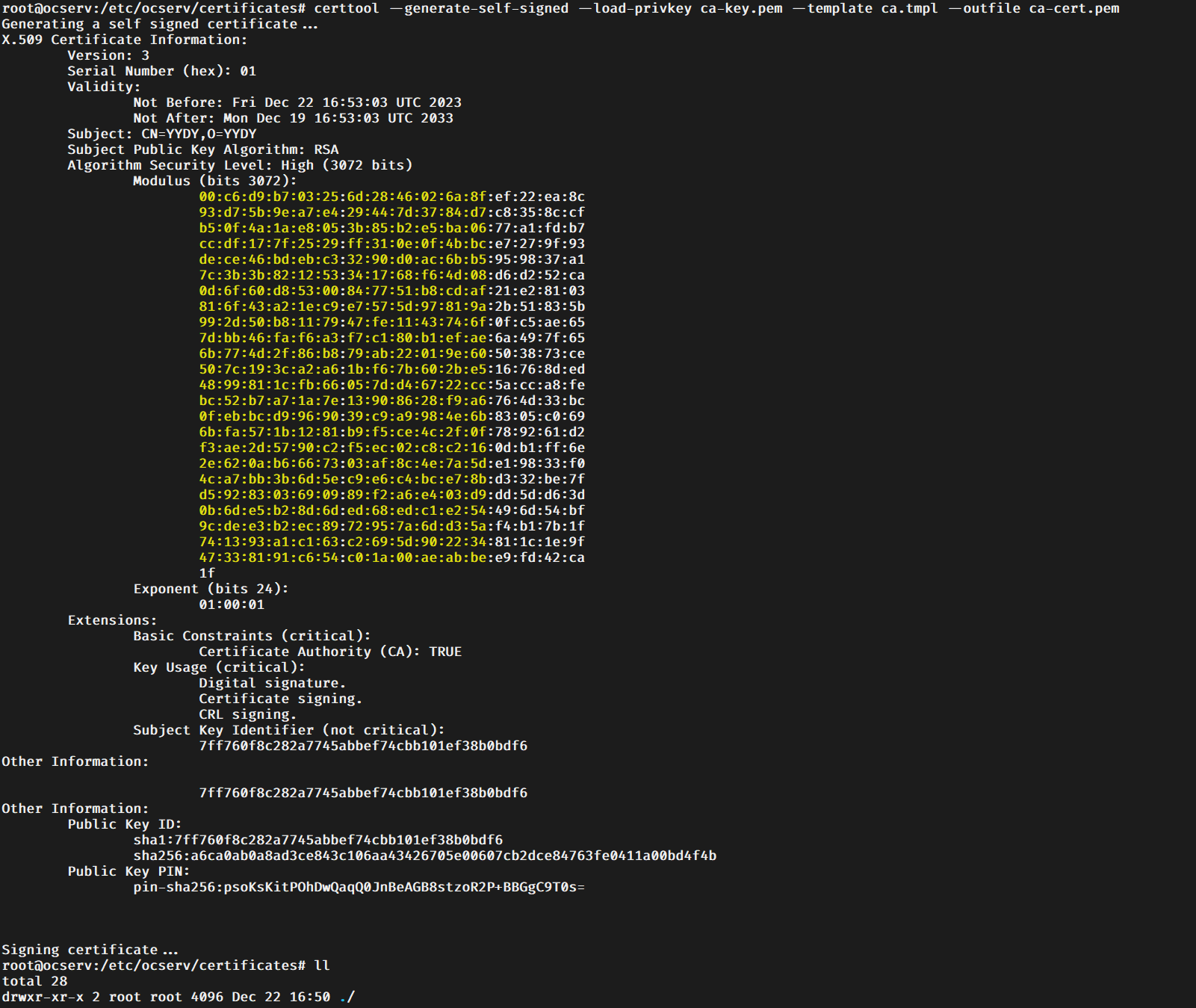
certtool --generate-self-signed --load-privkey ca-key.pem --template ca.tmpl --outfile ca-cert.pem
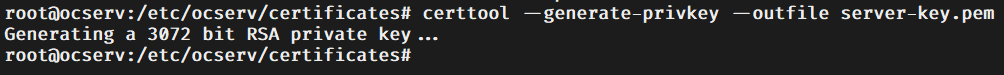
certtool --generate-privkey --outfile server-key.pem
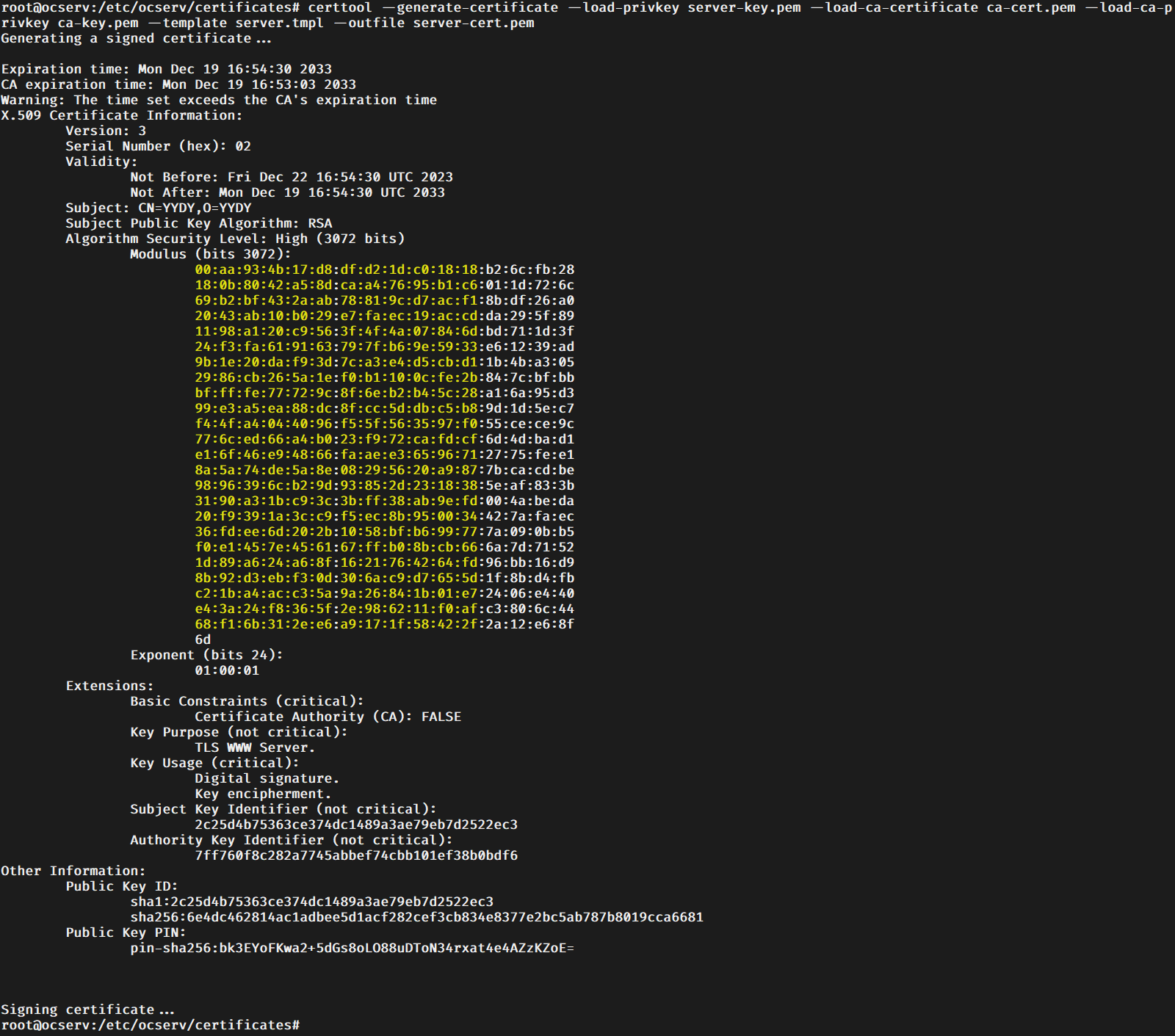
certtool --generate-certificate --load-privkey server-key.pem --load-ca-certificate ca-cert.pem --load-ca-privkey ca-key.pem --template server.tmpl --outfile server-cert.pem
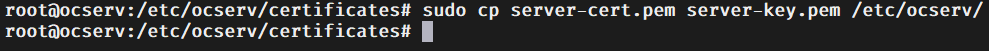
sudo cp server-cert.pem server-key.pem /etc/ocserv/
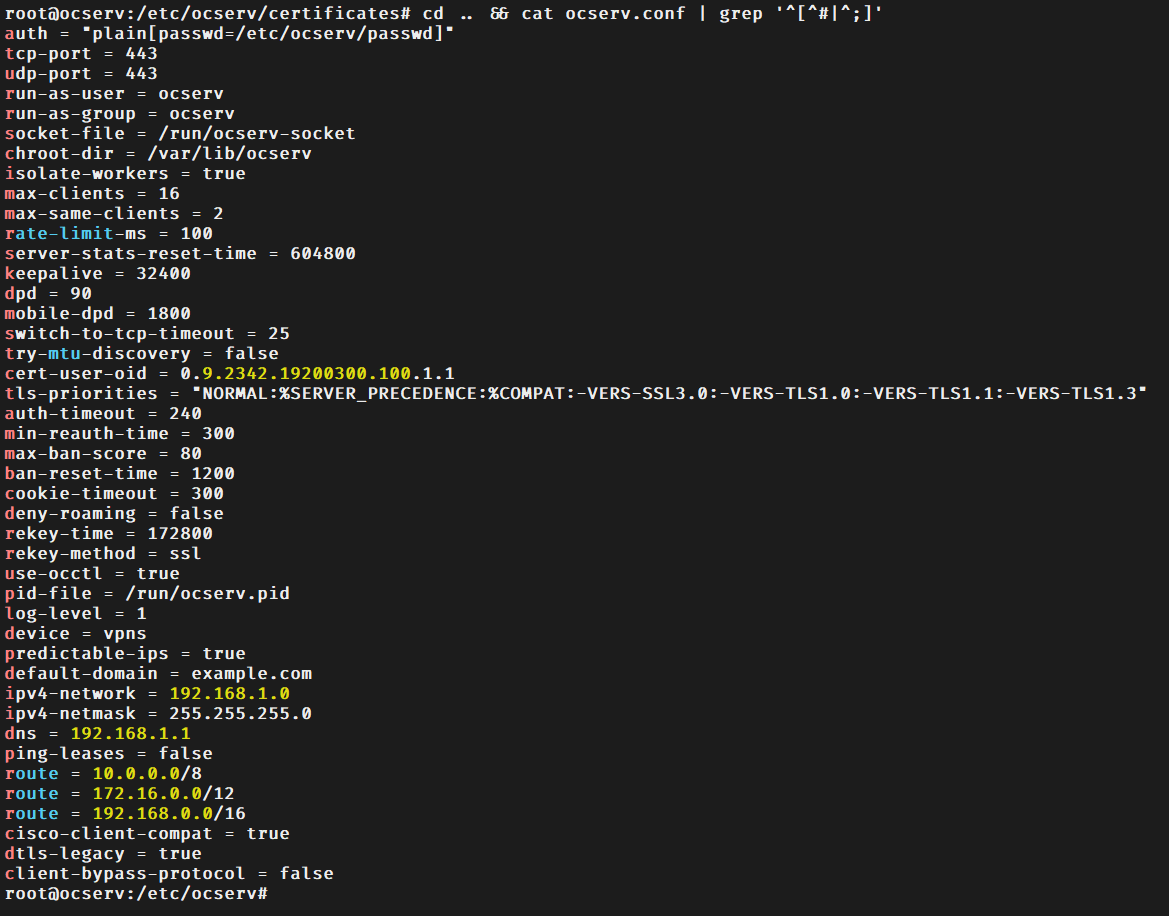
cd .. && cat ocserv.conf | grep '^[^#|^;]'
cd certificates && ll && pwd
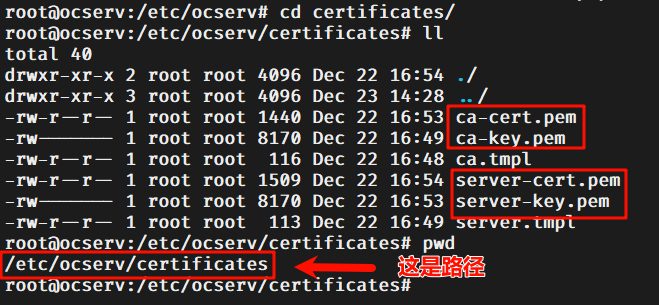
ca-cert = /etc/ocserv/certificates/ca-cert.pem
server-cert = /etc/ocserv/certificates/server-cert.pem
server-key = /etc/ocserv/certificates/server-key.pem
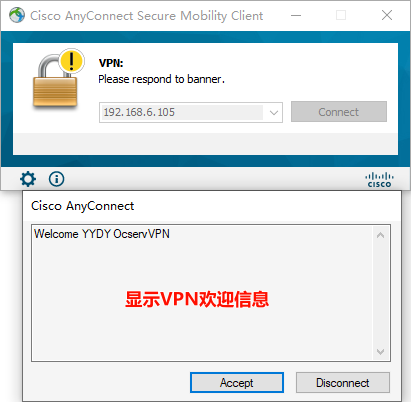
banner = "Welcome YYDY OcservVPN"
try-mtu-discovery = true
mtu = 1200
max-clients = 100
max-same-clients = 5
ipv4-network = 100.255.255.0
ipv4-netmask = 255.255.255.0
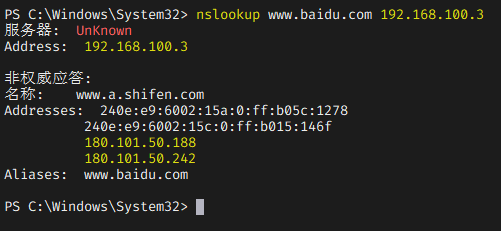
dns = 10.10.10.10
no-route = 10.0.0.0/255.0.0.0
no-route = 172.16.0.0/255.240.0.0
no-route = 192.168.0.0/255.255.0.0
route = 10.10.10.10/255.255.255.255
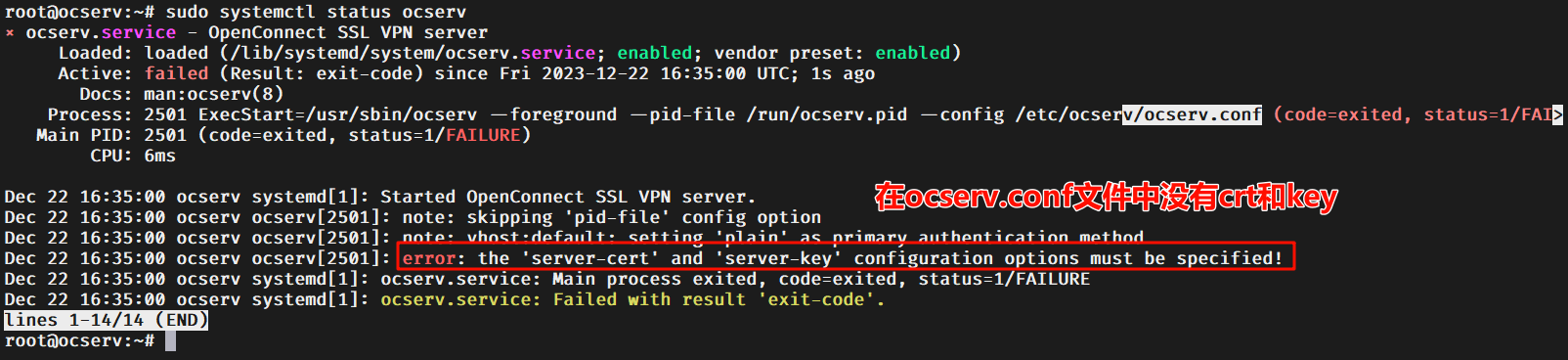
sudo systemctl restart ocserv.service
sudo systemctl status ocserv.service
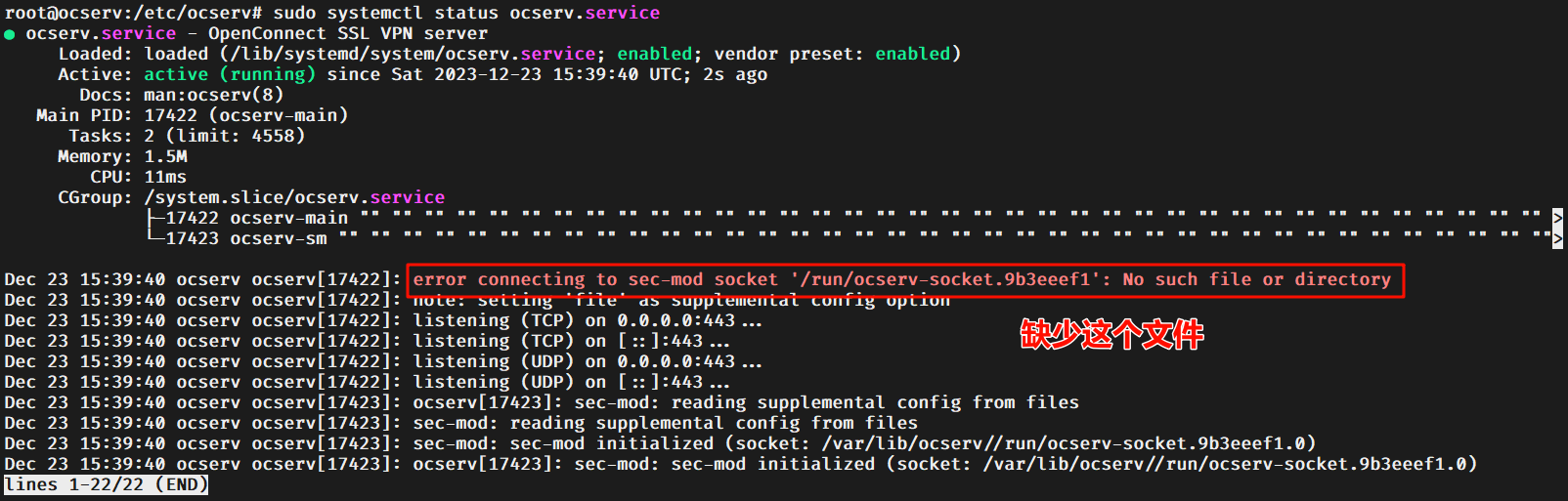
sudo touch /run/ocserv-socket
sudo chmod 660 /run/ocserv-socket
sudo chown ocserv:ocserv /run/ocserv-socket
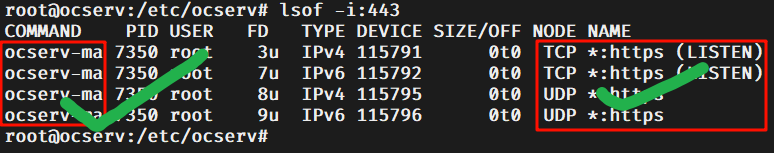
lsof -i:443
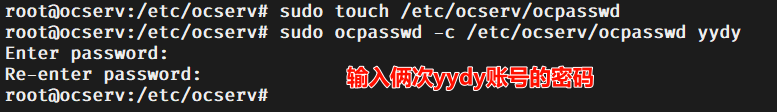
sudo touch /etc/ocserv/passwd
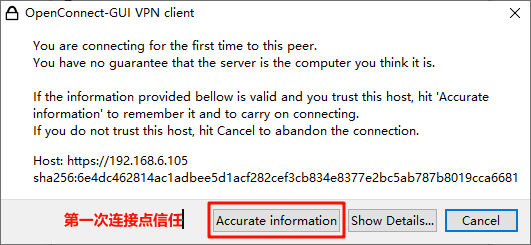
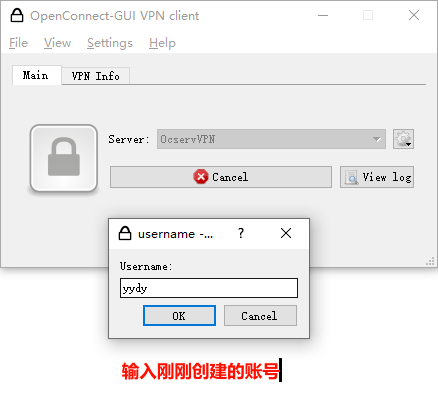
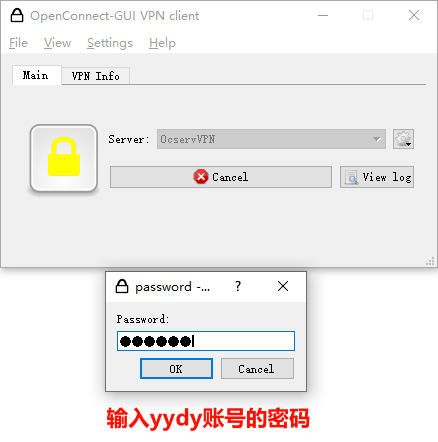
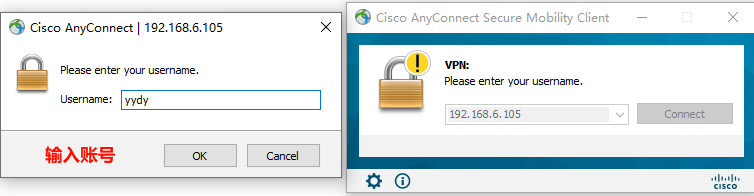
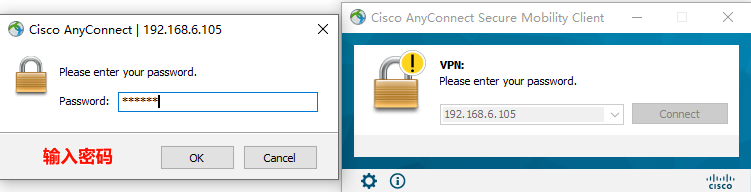
sudo ocpasswd -c /etc/ocserv/passwd yydy
sudo ocpasswd -c /etc/ocserv/passwd -d username
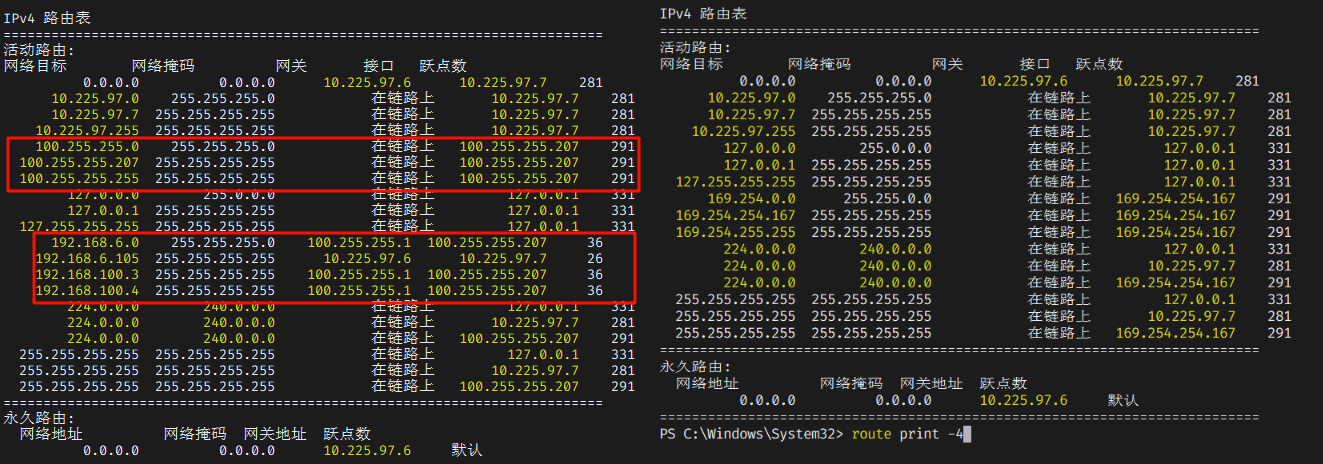
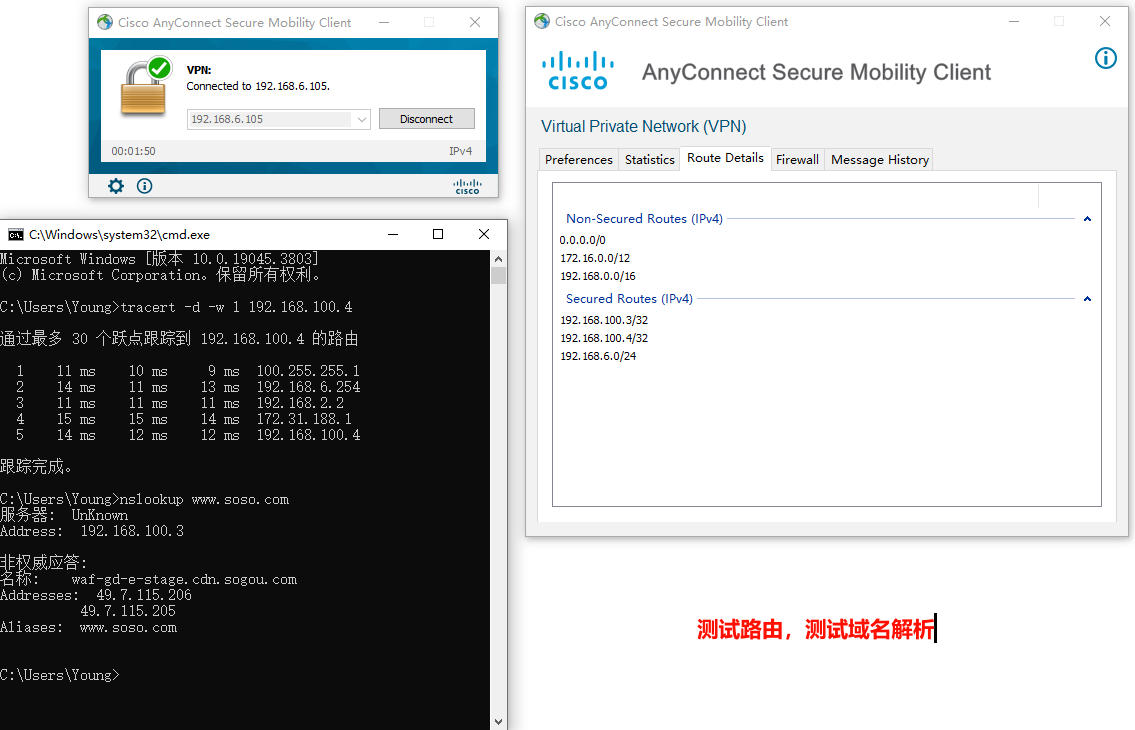
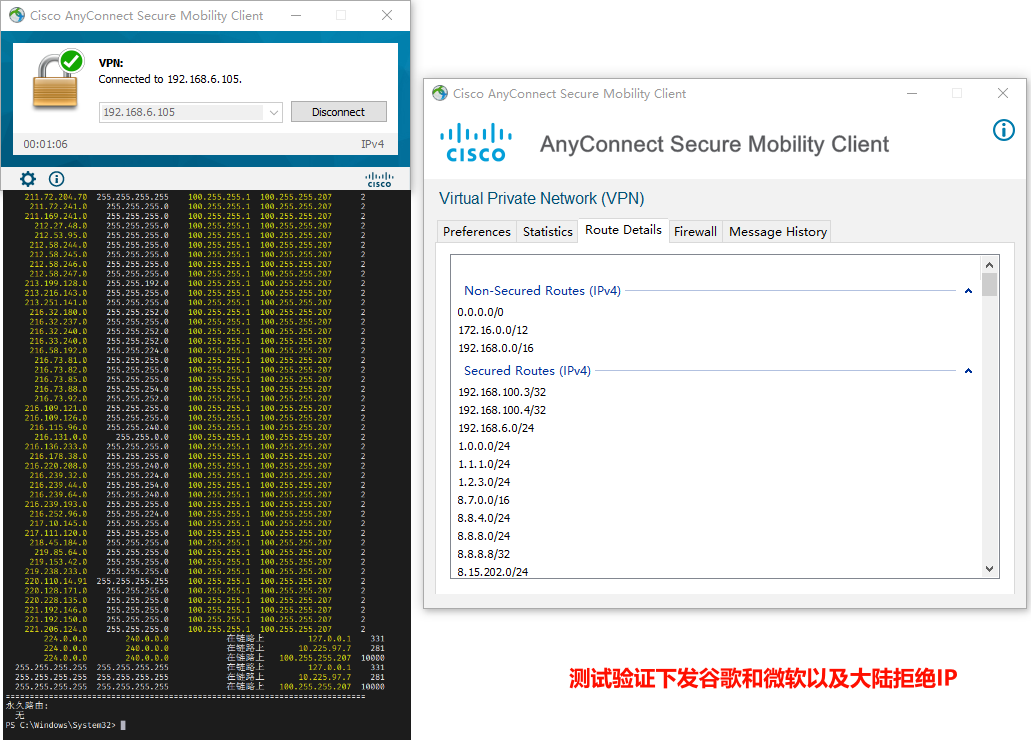
route print -4
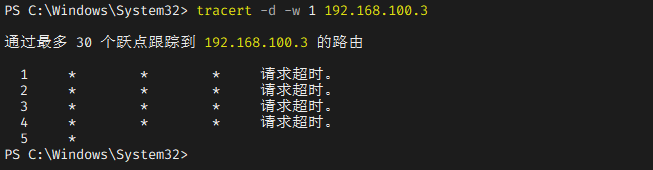
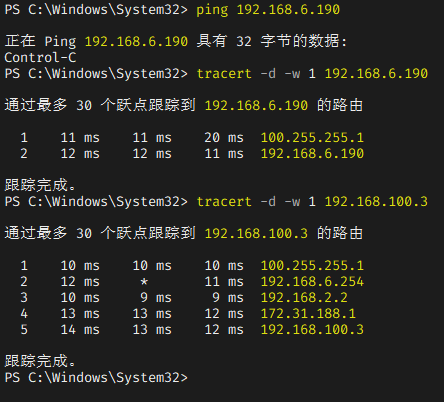
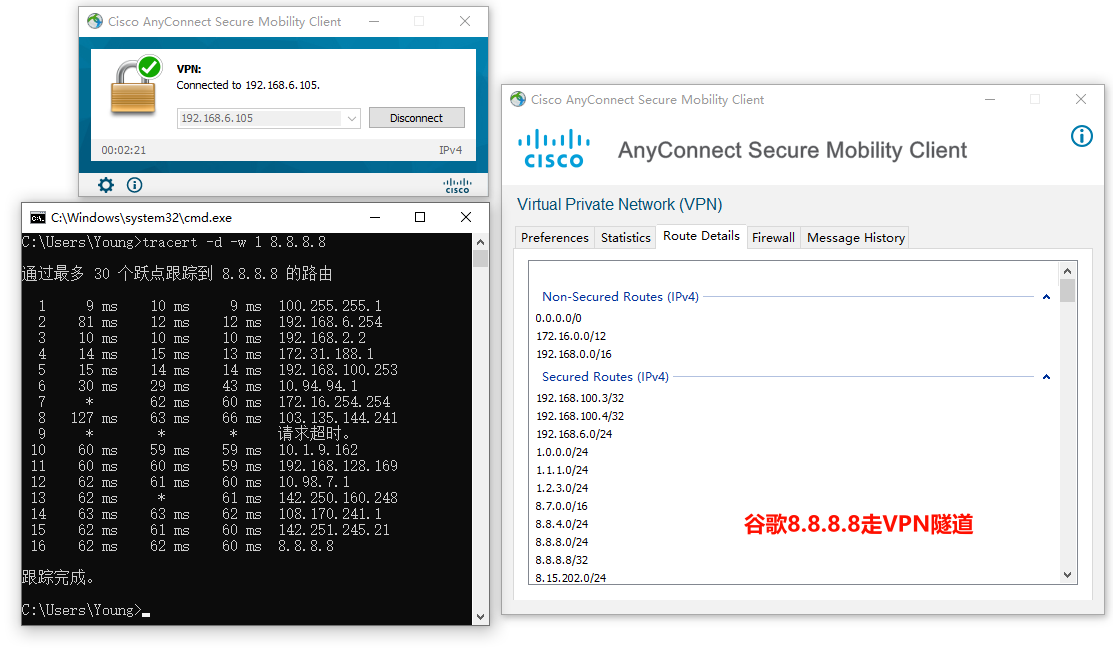
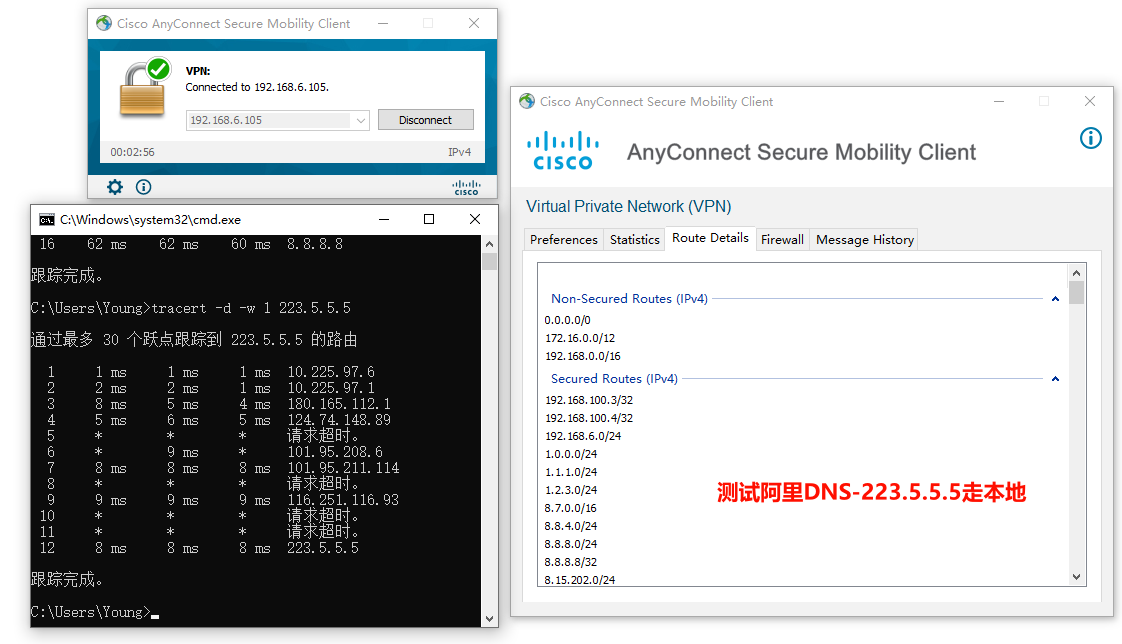
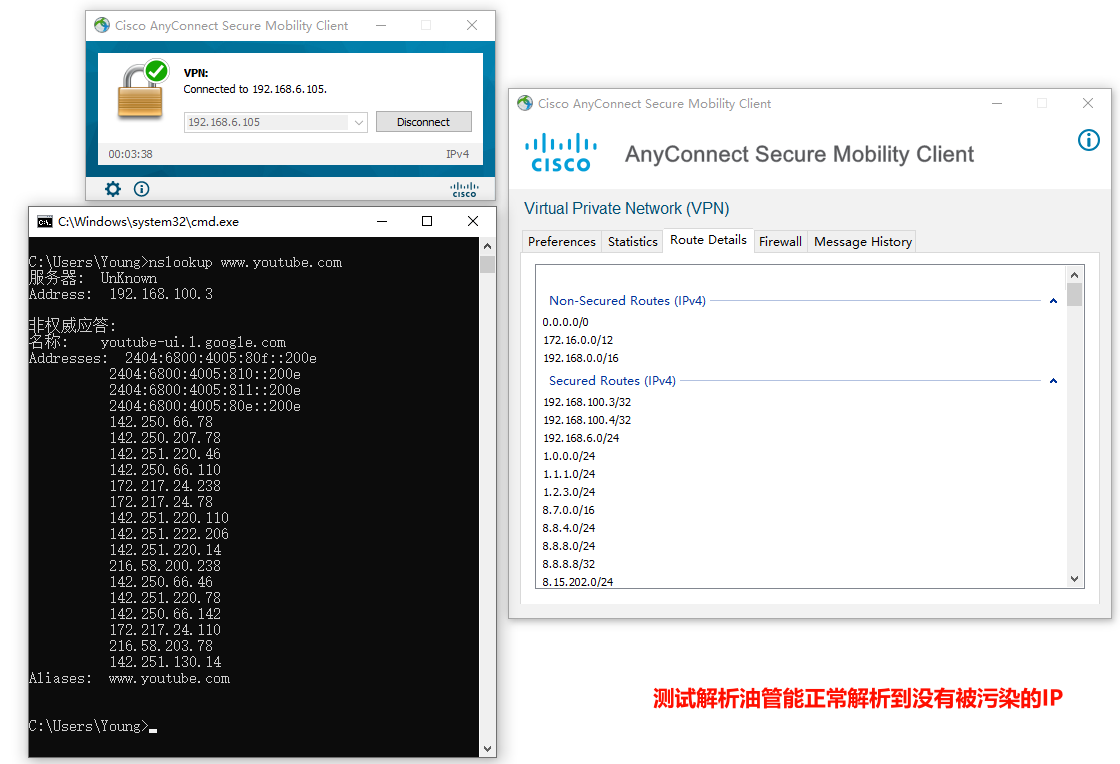
tracert -d -w 1 内网IP
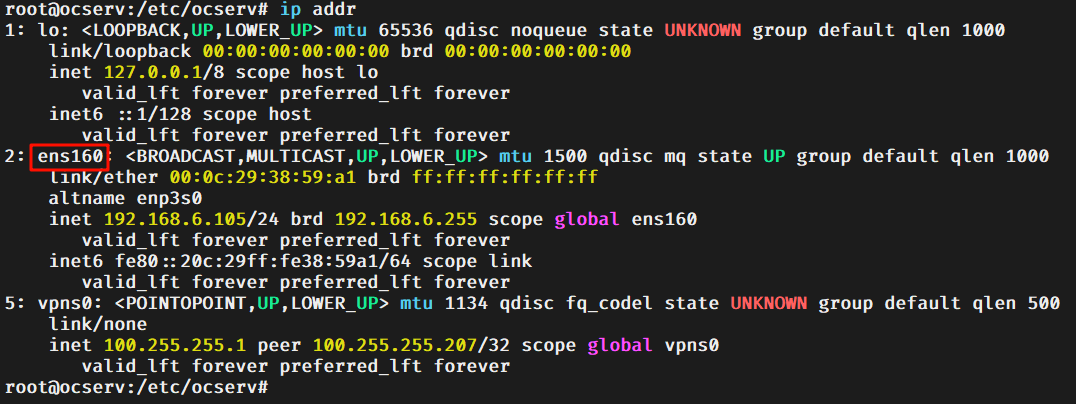
ip addr
sed -i '/net.ipv4.ip_forward/s/0/1/' /etc/sysctl.conf
sed -i '/net.ipv4.ip_forward/s/#//' /etc/sysctl.conf
sysctl -p
iptablessudo iptables -t nat -A POSTROUTING -o ens160 -j MASQUERADE
iptables-persistentsudo apt install -y iptables-persistent
iptables-persistentsudo netfilter-persistent save
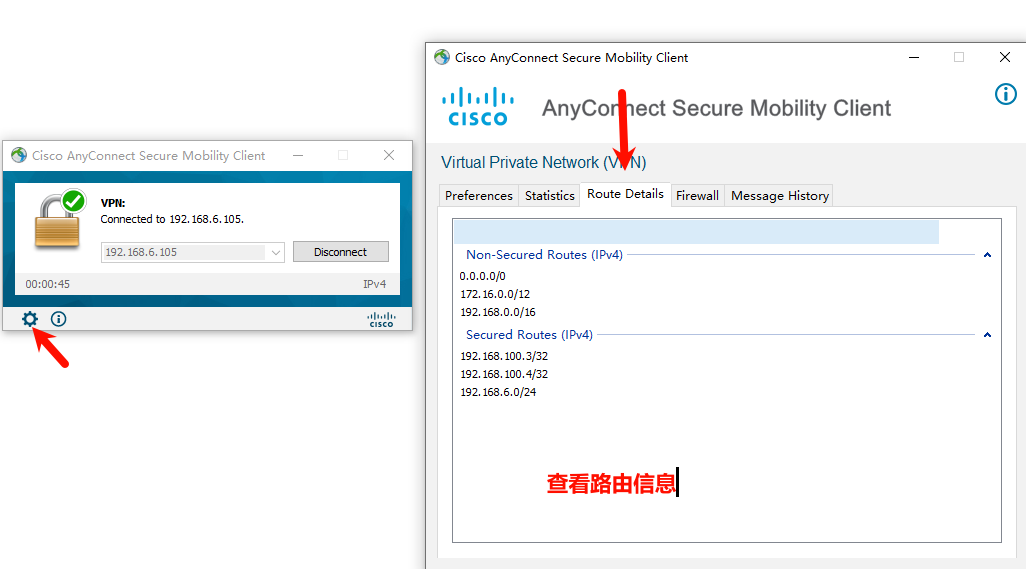
no-route = 10.0.0.0/255.0.0.0
no-route = 172.16.0.0/255.240.0.0
no-route = 192.168.0.0/255.255.0.0
route = 192.168.100.3/255.255.255.255
route = 192.168.100.4/255.255.255.255
route = 192.168.6.0/255.255.255.0
no-route = 10.0.0.0/8
no-route = 172.16.0.0/12
no-route = 192.168.0.0/16
route = 192.168.100.3/32
route = 192.168.100.4/32
route = 192.168.6.0/24


评论
发表评论